What is BIP32?
Bitcoin Improvement Proposal 32, or BIP32, is a protocol that introduced Hierarchical Deterministic (HD) wallets into the world of cryptocurrency. HD wallets are an essential upgrade over traditional wallets because they allow for the creation of child keys from a single parent key, meaning users can generate multiple unique addresses from a single seed.
Where did BIP32 come from?
BIP32 was proposed by Pieter Wuille, a Bitcoin Core developer, and released in February 2012. This proposal aimed to improve the limitations of traditional non-deterministic wallets, which required a new backup for each new address.
How does BIP32 Work?
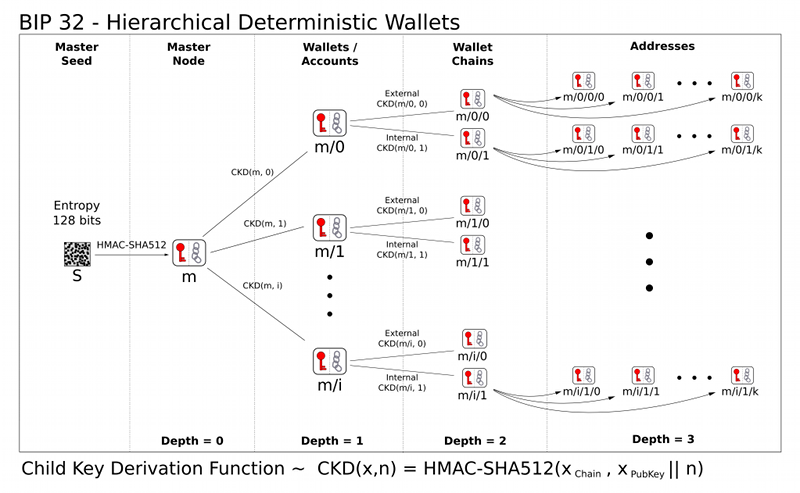
BIP32 introduces two important concepts: key derivation and the hierarchical tree structure.
- Key Derivation: In a BIP32 HD wallet, all the keys and addresses stem from a single root key known as the master private key. Child keys (both private and public) are derived from this root in a deterministic way, meaning you can always generate the same set of keys from the master key. This system also ensures privacy because public keys can be generated without revealing the corresponding private keys.
- Hierarchical Tree Structure: BIP32 allows keys to be organized in a multi-level tree structure. This means you can have child keys, grandchild keys, and so forth, organized in a hierarchical manner. It gives you the flexibility to manage funds across different branches (accounts, sub-accounts) under a single wallet.
Together, these two features make backups much simpler because a backup of the master key (or seed) is sufficient to recover all derived keys and addresses.
BIP32 and Trezor
Trezor hardware wallets use the BIP32 protocol as the backbone for the key management system. When a Trezor device is initialized, it generates a 12, 18, or 24-word recovery seed using BIP39. This seed becomes the master key for the BIP32 key derivation process.
Every time a user wants to create a new account or address in their Trezor wallet, BIP32 is used to derive new keys from the master seed. This means that users can handle multiple accounts and addresses, all linked to the original recovery seed.
The use of BIP32 offers significant benefits. Firstly, it greatly simplifies backup procedures, as users only need to secure their BIP39 recovery seed to ensure access to all their keys. Secondly, it enhances privacy by allowing users to generate new addresses for every transaction, making tracking more difficult. Lastly, the hierarchical structure allows users to organize their funds across different accounts and sub-accounts in a structured manner.
In conclusion, BIP32 has revolutionized the way wallets manage keys and addresses, making it easier for users to secure, recover, and organize their digital assets. By integrating BIP32, Trezor provides users with a safe, efficient, and user-friendly way to manage their cryptocurrencies.
Derivation Paths
BIP32 derivation path:
BIP32 extended private key represents the extended private key derived from the derivation path. An example of a BIP32 extended private key is:
Trezor and BIP32 address paths
Trezor uses BIP44, which is based on BIP32. BIP44 dictates the derivation path:
Overview of standard derivation paths of recovery seeds know by the latest Trezor firmware
Cryptocurrencies
BIP44-like paths (discoverable):
- m/44'/cointype'/account'/change/address ... BIP44 P2PKH
- m/49'/cointype'/account'/change/address ... BIP49 P2WPKH-nested-in-P2SH
- m/84'/cointype'/account'/change/address ... BIP84 P2WPKH
BIP44-like paths (non-discoverable):
- m/48'/cointype'/account'/change/address ... multisig P2SH, implemented in Copay wallet, no BIP or SLIP defined
Others:
- m/48'/network'/role'/account'/key' ... SLIP48 Graphene-based blockchains
Custom cryptography
- m/13'/A'/B'/C'/D' ... SLIP13 Sign in with Trezor
- m/17'/A'/B'/C'/D' ... SLIP17 ECDH
- m/10015'/0' ... SLIP15 Trezor Wallet labeling metadata
- m/10016'/0 ... SLIP16 Trezor Password Manager metadata